RISK INTELLIGENCE
1. Permissions Discovery
Help ensure that only authorized individuals can access sensitive data.
This includes:
• Inappropriate permission discovery
• Support for multiple file types
• Granular permission scans
• Information on leaked or stolen data
2. Personally Identifiable Information and Protected Health Information Discovery
Safeguard sensitive personal data from attack.
This includes:
• Personally identifiable information discovery
• Payment data discovery
• Deep scans in hard-to-find persistent storage
• Customizable scans
3. Risk Intelligence Reports
View reports on the potential financial impact of your at-risk data.
This includes:
• Credit card data discovery
• Establishing a data breach risk baseline
• Vulnerability trend report
• Data breach risk trend report
• Per-device breakdowns of insecure data
• Custom report branding
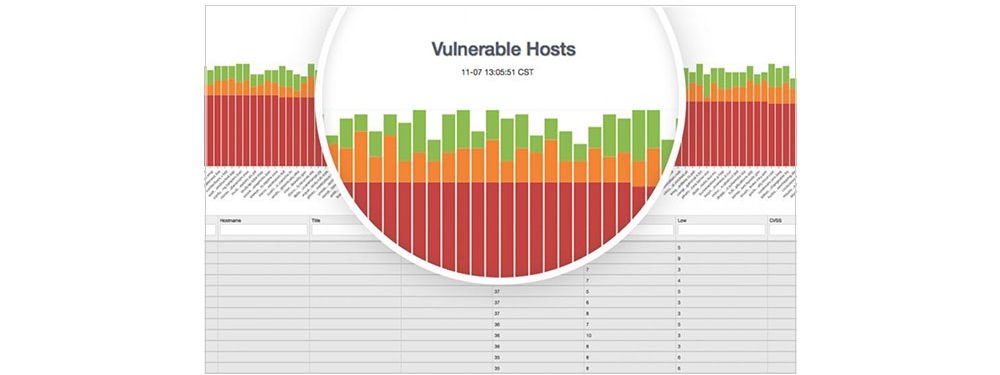
4. Vulnerability Scanning
Locate Security Holes in Your Systems.
This Includes:
• Host-based scanning
• Lightweight scans
• Emerging threat discovery
• Cross-device search
• Unpatched software
• E-mail
• Mac and Windows operating systems vulnerabilities
• Threats from VPN connections
5. Payment Data Discovery
Protect credit card data and help ensure PCI DSS compliance.
This includes:
• PCI DSS required scans
• Multiple supported device types
• Encryption for data-in-transit and data-at-rest
• Extensive file types for multiple technologies
• Cross-platform compatibility